Secure APIs with FastAPI and the Microsoft Identity Platform Course
If you are a Python developer that wants to know how to implement secure, JWT-based authentication and authorization by leveraging a scalable, secure and flexible identity provider such Azure AD, then this course is for you. You will learn how to secure your APIs without the need to write too much code or having intricate knowledge on how OAuth2 and OIDC work. A plug and play solution for every Python developer and solution architect out there.
What students are saying
Source code and course GitHub repository
github.com/talkpython/fastapi-and-the-microsoft-identity-platform-courseWhat's this course about and how is it different?
Identity and security are complex topics. Your solution is as secure as the weakest link in your code. Instead of spending weeks or even months building an identity solution for your application, it’s highly recommended that you use a battle-tested Identity Provider such as Azure Active Directory. Azure AD handles billions of authentications daily and scales from 1 user to millions users without you having to think about performance, storage, backups, and availability.
This is the only course (that we’re aware of) that shows you how to add authorization to your Fast API and implement strict checks on JWT Access Tokens to validate incoming requests. In this course, you’ll learn how end-to-end scenarios work in real life scenarios by building clients that can securely authenticate and call our FastAPI-based application. Finally, you'll spend some time learning general identity principles and do a deep dive on why and how JWT-based authentication is more secure.
After completing this course, you’ll have a robust understanding of how to build modern, secure solutions with Python, FastAPI, and Azure Active Directory.
Prerequisite course
While the code written in this course is simple and you only need basic fluency with Python, we do assume you know FastAPI. If you're entirely new to FastAPI, please consider taking our Modern APIs with FastAPI and Python to become comfortable with FastAPI first.
What topics are covered?
In this course, you will:
- Learn what Identity is and why modern solutions need to know who we are and what we can do.
- Understand modern authentication and why we needed open standards such OAuth2 and OpenID Connect (OIDC).
- Learn how to create and work with Microsoft Azure Active Directory.
- Take a look at the
microsoft_identity_fastapipackage built specifically to perform authorization and token validation in FastAPI-based solutions. - Dive deep into JWT-based authentication and better understand tokens and claims.
And lots more.
View the full course outline.
Who is this course for?
This course is for anyone who creates APIs with the FastAPI framework in Python and needs to add the necessary security to protect access to sensitive resources and data but doesn’t want to (and shouldn’t have to) build and maintain their own identity service. A key benefit of this approach is that you need to do very little to implement authentication and authorization in FastAPI - it’s literally a few lines of code and some configuration and you’re ready to go.
The experience level for anyone taking this course is very light high. You’ll need:
- A basic understanding of how Fast API works.
- Experience with core Python concepts (such as classes, functions, variables etc).
- Knowledge of API clients such as Postman etc.
Note: All software used during this course, including editors, the Azure AD service, Python language, etc., are 100% FREE. You won't have to buy anything to take the course.
Follow along with subtitles and transcripts
Each course comes with subtitles and full transcripts. The transcripts are available as a separate searchable page for each lecture. They also are available in course-wide search results to help you find just the right lecture.
Who am I? Why should you take my course?
 Hi everyone, my name is Christos and it’s nice to meet you.
Hi everyone, my name is Christos and it’s nice to meet you.
There are a couple of reasons why I’m especially qualified to teach you about security and identity.
- I’m a senior PM at Microsoft where I work as developer advocate with a special focus on helping developers and enterprises of any size to build robust, scalable and, most of all, secure solutions. I’m particularly passionate about security and this is why I want to help the developer community.
- I’ve been a professional developer for almost 20 years. I have worked with 1000s of companies of every size building all types of software and teaching developers how to follow best practices.
- I’m not here to sell you anything. Although I work for Microsoft, the principals taught in this course are based on open standards and are transferable to other cloud providers and platforms.
- I hope that you’ll appreciate and enjoy my course and even if you don’t, I’m always happy to hear your feedback and suggestions on how I can make it better for you.
Free office hours keep you from getting stuck
One of the challenges of self-paced online learning is getting stuck. It can be hard to get the help you need to get unstuck.
That's why at Talk Python Training, we offer live, online office hours. You drop in and join a group of fellow students to chat about your course progress and see solutions via screen sharing.
Just visit your account page to see the upcoming office hour schedule.
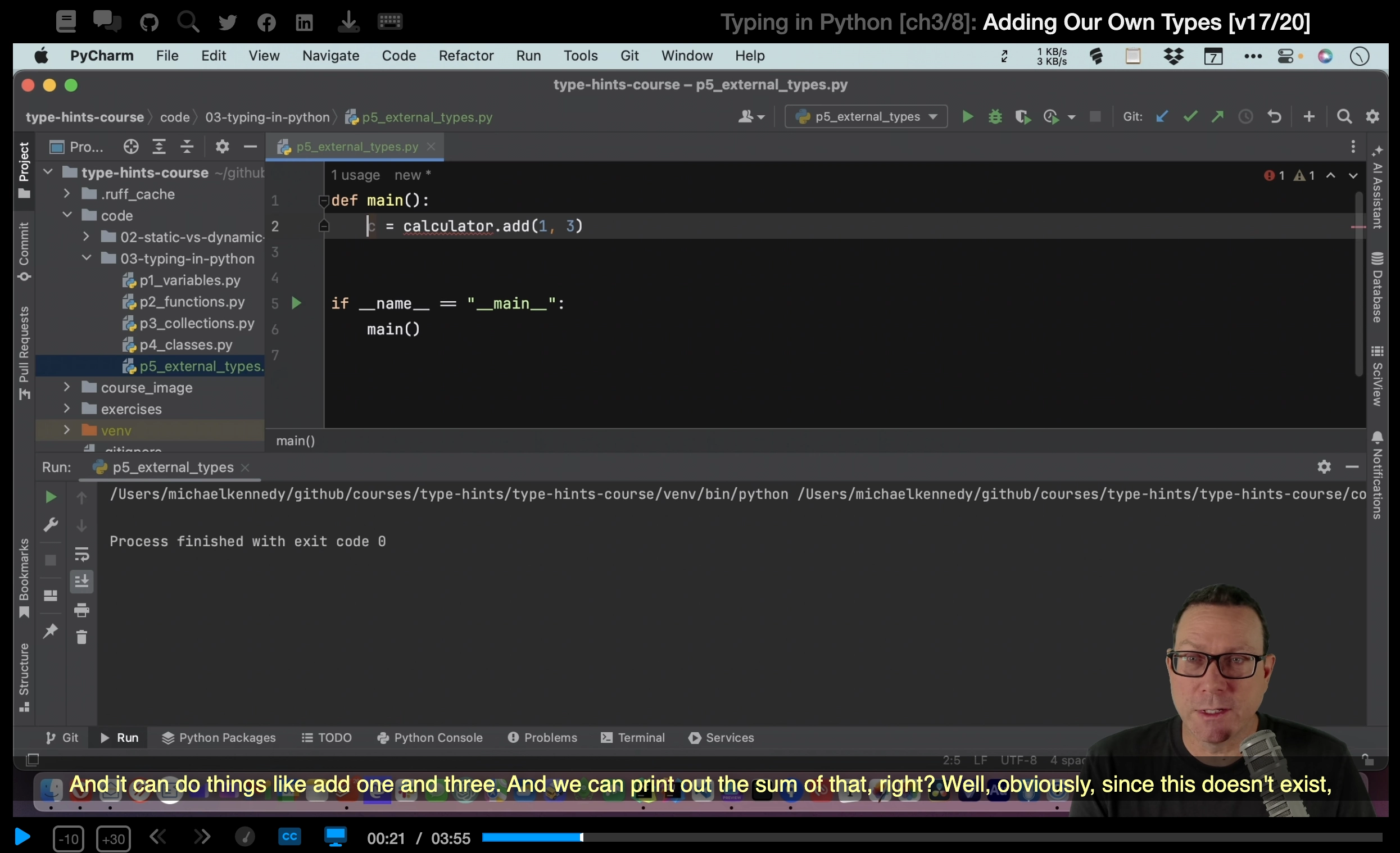
This course is delivered in very high resolution
This course is delivered in 1440p (4x the pixels as 720p). When you're watching the videos for this course, it will feel like you're sitting next to the instructor looking at their screen.
Every little detail, menu item, and icon is clear and crisp. Watch the introductory video at the top of this page to see an example.
Is this course based on Python 3 or Python 2?
This course is based upon Python 3. Python 2 is officially unsupported as of January 1st, 2020 and we believe that it would be ill-advised to teach or learn Python 2. This course is, and has always been, built around Python 3.
The time to act is now
If you need a more modern way to authentic API clients than simple username and password or api key schemes, this course is for you. Especially if you're focused on the Microsoft cloud stack or Azure Active Directory. Take the course today!
Course Outline: Chapters and Lectures
| 4:53 | ||
|
|
transcript | 1:19 |
|
|
transcript | 1:19 |
|
|
transcript | 1:01 |
|
|
transcript | 1:14 |
| 15:34 | ||
|
|
transcript | 3:17 |
|
|
transcript | 3:19 |
|
|
transcript | 3:36 |
|
|
transcript | 2:04 |
|
|
transcript | 3:18 |
| 20:38 | ||
|
|
transcript | 2:24 |
|
|
transcript | 4:59 |
|
|
transcript | 5:00 |
|
|
transcript | 8:15 |
| 31:54 | ||
|
|
transcript | 3:27 |
|
|
transcript | 15:19 |
|
|
transcript | 13:08 |
| 26:28 | ||
|
|
transcript | 4:35 |
|
|
transcript | 11:24 |
|
|
transcript | 6:23 |
|
|
transcript | 4:06 |
| 4:49 | ||
|
|
transcript | 0:34 |
|
|
transcript | 0:58 |
|
|
transcript | 1:25 |
|
|
transcript | 0:50 |
|
|
transcript | 0:33 |
|
|
transcript | 0:29 |